Is HappyMod Safe? 2026 VirusTotal Scans & Ban Risk Guide
HappyMod safety requires 3 separate verdicts because the platform has 3 components with 3 distinct risk profiles. One answer covers none of them accurately. The verified HappyMod APK with its SHA256 hash and 0/65+ VirusTotal result is published on the HappyModdAPK.net — the verification methodology behind those results is documented on the APK verification page.
This page documents what those results mean for each safety decision, what the catalog mod risk profile looks like, and how account ban risk stratifies by game type.
Reviewed by: Muhammad Sheraz | APK Reviewer, HappyModdAPK.net
Test Devices: Samsung Galaxy A54 (One UI) | Redmi Note 12 (MIUI) | OnePlus 12 (OxygenOS) | Realme 11 Pro (Realme UI)
Is the HappyMod APK installer file safe?
Yes. The current stable release returned 0/65+ VirusTotal detections. Muhammad Sheraz confirmed installation on four Android devices with zero unexpected permission requests. Every platform build on this site passes six verification checks before the download button activates.
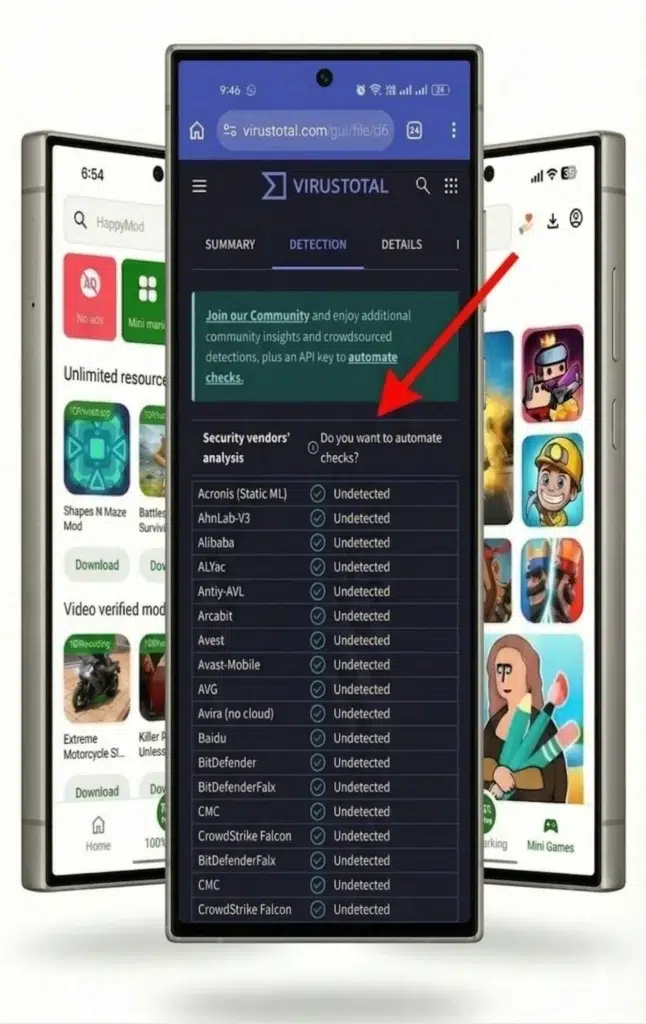
What the 0/65+ VirusTotal result means for the safety decision
Zero detection means no known malware signature matched the file across 65+ engines at the time of scan. For the safety decision whether to download and install HappyMod a 0/65+ result from a named, dated scan with a published hash represents the strongest publicly available evidence that the installer file is clean.
Two limitations apply to this result that affect the decision. First: the result is point-in-time. A scan from 6 months ago carries less weight than a scan from the current review cycle. The scan date appears alongside the result on the HappyMod APK main page.
Second: VirusTotal and SHA256 are static analysis tools they examine the file before it runs. They do not observe what an app does after installation. The behavioral risk from post-installation code execution is covered in Section 2.
Users who want to run their own verification generating the SHA256 hash and comparing it against the published value can follow the step-by-step process on the APK verification page.
The 6-step verification process
Are the mods downloaded through HappyMod safe?
Catalog mods carry variable safety. Each of the 200,000+ catalog entries is community-submitted. Muhammad Sheraz verifies the HappyMod APK installer not individual catalog mods. Mod safety at the decision level depends on 3 signals: working rate, recent user comment behavior, and the permission set each mod requests at installation.
The working rate distinction – functionality vs safety
HappyMod’s working rate calculates the percentage of users who report a build installs and runs correctly. A rate above 90% with a high submission count indicates strong community confidence in the build’s functionality. A rate below 50% signals frequent failure reports.
The working rate measures whether a mod works – not whether it is safe. A build with a 100% working rate installed on 500 devices can still contain behavioral components that users do not report because they are not visually observable. Community members report crashes, missing features, and incorrect behavior. They rarely report background network activity, permission elevation attempts, or data transmission events that require monitoring tools to observe.
This distinction determines how the working rate fits into the safety decision: it is a required signal, not a sufficient one. A mod below 75% working rate warrants skipping regardless of safety. A mod above 90% working rate still requires permission review at installation.
Dynamic Code Loading – the behavioral risk no pre-install check detects
Some modified APK files pass VirusTotal scans at zero detections at the time of download because the harmful behavior is not present in the downloaded file. These files download and execute additional code from a remote server after the app first launches – a technique called Dynamic Code Loading (DCL). The code fetched post-installation does not exist in the file that static analysis tools scan.
For the catalog mod safety decision, DCL means: a clean pre-install scan result reduces risk but does not eliminate it for community-submitted catalog mods. Behavioral evidence from users who have run the mod for several days on real devices – recent user comments in the catalog listing – provides the only available post-installation safety signal outside of running dedicated network monitoring tools.
This is why recent user comments carry more safety relevance than the working rate percentage alone. A user who reports running a mod for 14 days with no unexpected ads, no unusual battery drain, and no permission escalation provides behavioral evidence that a VirusTotal scan cannot.
The automated submission scanning layer
HappyMod runs each catalog submission through an automated security scan before it appears in the catalog. Builds that fail this scan are blocked. HappyMod reviews flagged submissions and removes those confirmed as unsafe.
This layer reduces the volume of clearly malicious files in the catalog but shares the same static analysis limitation as all pre-install scanning tools – it cannot catch DCL-based behavioral risks or post-installation runtime behavior.
How do I decide whether a specific HappyMod mod is safe to install?
Apply a 4-checkpoint decision sequence before every catalog mod download: working rate above 75% with a sample above 100 reports, user comments from the past 7 days confirming clean behavior, a permission set matching the mod’s core function at installation, and a base version that matches the current game version on the device.
Checkpoint 1 – Working rate and sample size
A working rate above 90% with more than 100 submission reports provides strong community confidence. Between 75% and 89% warrants reading recent comments before deciding. Below 75% indicates frequent failures skip this build and check for an alternative submission of the same mod.
A high percentage from fewer than 20 reports is statistically unreliable small sample sizes produce volatile percentages that shift dramatically with a handful of reports.
Checkpoint 2 – Comment recency and behavioral content
User comments from the past 7 days reflect current device behavior on the current game version. Read the most recent 5-10 comments specifically for: mentions of ads appearing outside the app after installation, unexpected permission prompts during or after installation, battery drain or background data anomalies, and confirmation that the mod’s described feature actually activated.
A mod where recent comments confirm clean behavior and feature activation over multiple days represents the lowest available risk profile for a community-submitted file.
Checkpoint 3 – Permission evaluation at installation
Every mod requests its own permission set at the Android installation screen, separate from HappyMod’s own 4 permissions. Review this list before tapping Install. A game mod requesting Storage, Internet Access, and Vibration matches a normal function set for an offline game.
Any request for camera, microphone, contacts, location, or SMS warrants immediate cancellation these 5 permission types have no legitimate function in any standard game modification. The complete red-flag permission framework is documented on the HappyMod app permissions page.
Checkpoint 4 – Base version alignment
A mod built against game version 1.20 installed on a device running game version 1.21 may produce behavioral inconsistencies when the game accesses code paths the mod was not built against. The listing details panel in HappyMod shows the base version the mod was compiled against.
Confirm this matches the game version installed on the device. A version mismatch does not indicate malware but indicates functional incompatibility and potentially unpredictable runtime behavior.
Will using HappyMod mods get my account banned?
Account ban risk depends entirely on the mod type. Online multiplayer games detect modified clients through Play Integrity API and server-side behavioral analysis detection produces immediate permanent bans. Strictly offline games carry substantially lower risk because no server-side detection runs during use. Risk is not zero for any mod category.
How online multiplayer games detect modified clients
Online multiplayer games use 2 detection mechanisms. The first is Play Integrity API Google’s device and app integrity verification system that evaluates whether the running application matches the developer’s published version. A modified APK fails this check because its signature and binary content differ from the Play Store release.
The second is server-side behavioral analysis the game server compares player state values (resources, speed, position) against expected ranges and flags statistical impossibilities. Both mechanisms detect modified clients regardless of whether the device is rooted.
Detection typically occurs within the first multiplayer session. Server-side behavioral analysis is continuous it does not require a one-time integrity check at session start. A ban issued by either mechanism is permanent in most competitive multiplayer games and affects all purchased content, ranked progress, and history on the banned account.
The 3-level risk stratification by mod type
The secondary account strategy for Level 2 and Level 3 mods
Users who choose to use modified builds in games with any server contact should use a dedicated secondary account with no linked payment method and no purchased content. A banned secondary account loses free progress only.
A banned primary account loses all purchased items, currency, and ranked history none of which is recoverable regardless of ban appeal outcome. This strategy reduces the consequence of detection, not the probability.
Is HappyMod legal to use?
Using the HappyMod platform is not illegal in any jurisdiction. Individual mod content that distributes copyrighted game assets may constitute IP violation in jurisdictions without personal use exemptions. Using modified builds in games violates terms of service this is a contractual breach, not a legal violation.
Platform access vs content legality vs terms of service
These 3 categories require separate assessment because they carry different legal weights and different consequences.
Platform access
Platform access downloading the HappyMod installer, browsing the catalog, and downloading individual mods falls under normal software use in every major jurisdiction. No court has issued a finding that using a third-party APK repository constitutes an independently illegal act.
Content legality
Content legality applies to specific mod files that redistribute copyrighted game assets original artwork, music, or story content owned by the developer. Redistribution of these assets may constitute copyright infringement under IP law in jurisdictions without a personal use exception.
Most users download for personal use, which carries different legal exposure than commercial redistribution. The practical risk of legal action against individual users for personal use mod downloads is negligible in every reviewed jurisdiction developers pursue platform level action, not individual user action.
Terms of service violation
Terms of service violation is a contractual matter between the user and the game developer. Breaking a game’s terms of service by using a modified build produces account termination documented in Section 4 not legal liability. Competitor pages that call HappyMod illegal are mischaracterizing a contractual breach as a legal violation. These are not the same thing.
Is HappyMod safe for children and younger users?
HappyMod is appropriate for younger users with 3 safeguards: restrict downloads to strictly offline games with working rates above 90%, verify each mod’s permission set before installation, and use a secondary account with no real-money purchases for any online game. The platform itself contains no age-inappropriate content.

